What is email spoofing?
Email spoofing is a technique used by hackers to gain access and plant malwares into your system by altering the email header to impersonate a legitimate or trusted organization or person. The trick here is get the recipient to open and respond to the email when they see the sender is someone they know and trust. This article provides an overview of email spoofing, including how to identify and avoid email spoofing.
Why is email spoofing dangerous?
Although email spoofing can be easily resolved by simply deleting the emails, many people fall into the trap because the source of the email, as shown in the email headers, appears to be from a legitimate and trustworthy source. The contents of the emails are typically well-crafted, making it difficult for users to identify a fraudulent email. Many people will follow the instructions in the email, disclosing personal information, banking information, or clicking on any links in the email, allowing hackers to gain access into the user's system simply because the email headers appear to be valid.
How to identify email spoofing?
Following are some of the steps to help identify email spoofing:
- Check the email address and not just the display name. Hover over the display name and verify the email address.
- Check the received field , a new received field is added to the email header every time an email is sent.The email address should match the sender email address:
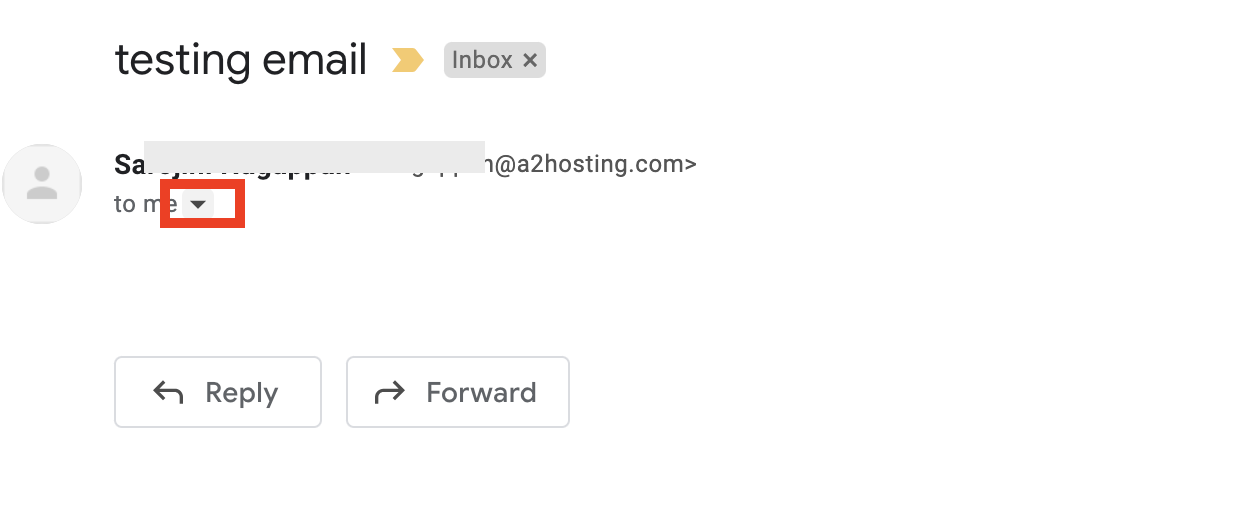
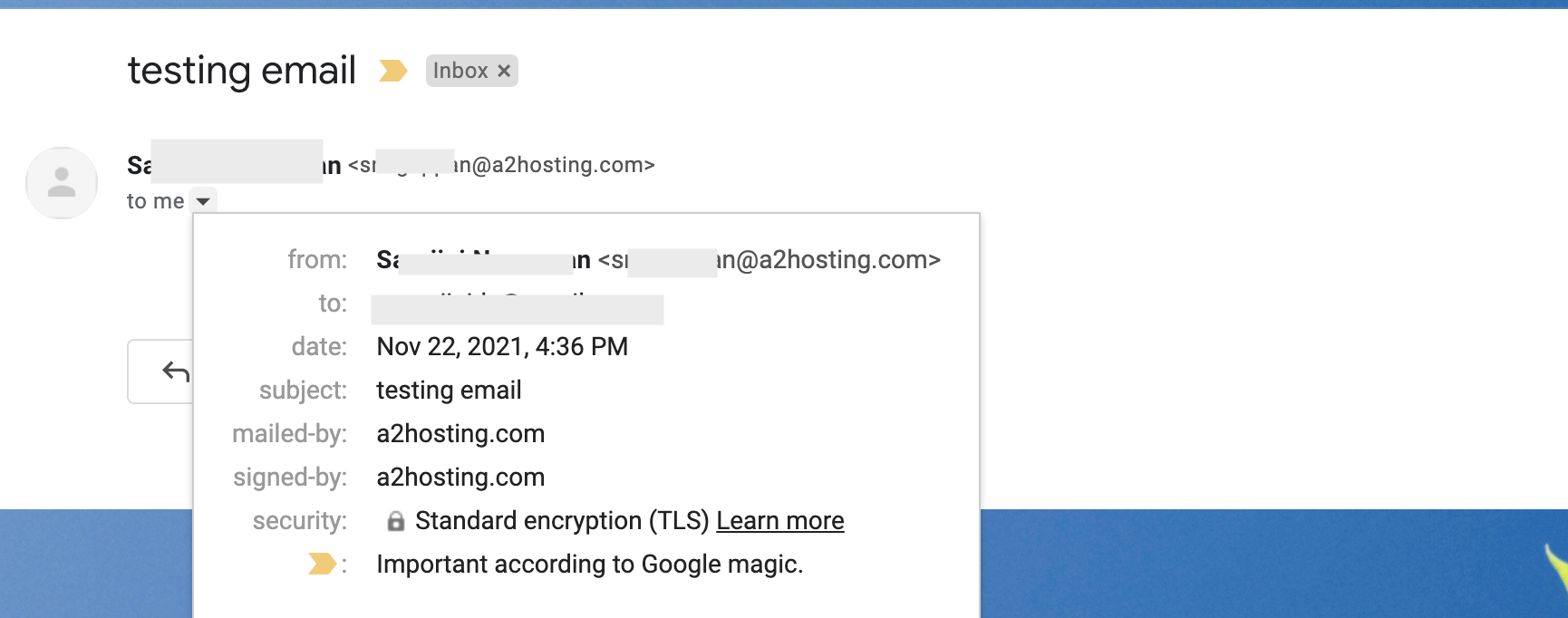
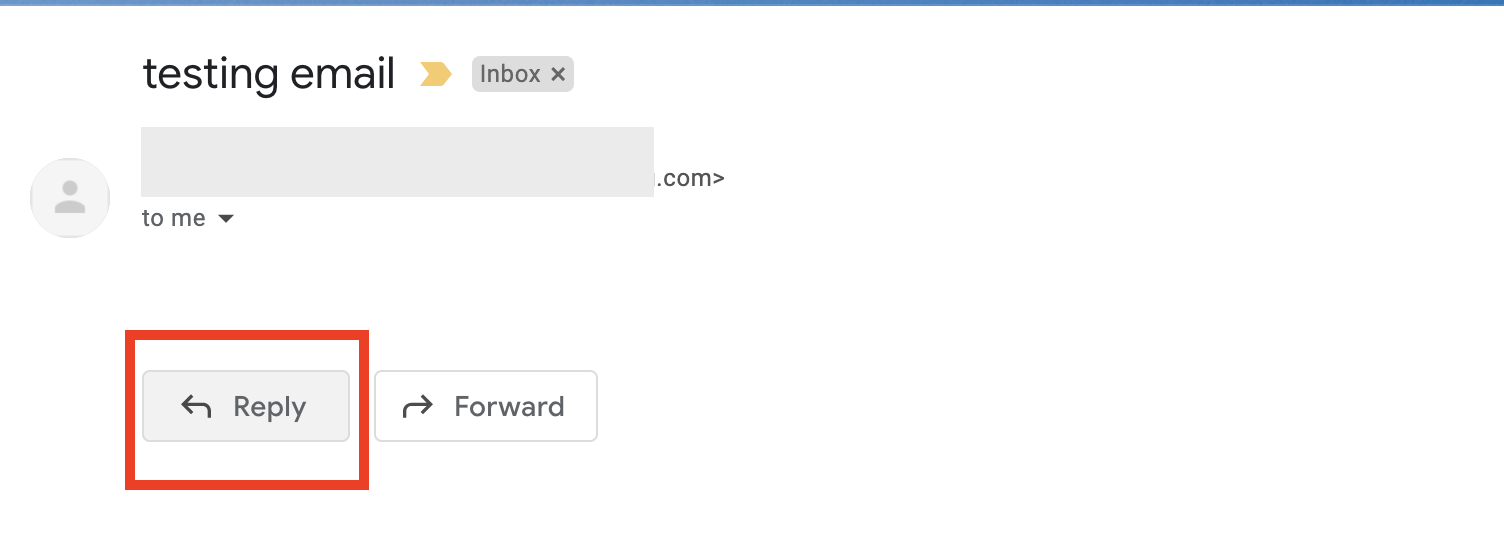
Check the reply path, when you click on reply, the email address must match the sender name in the original email:
- Check the tone of the content.
What is the difference between email spoofing and email phishing?
Phishing emails typically request personal information such as credit card numbers or pin numbers, or they collect user information through a pop-up notification requesting the user to click and fill out the details. Spoofing emails use false email headers and IP addresses to entice users to provide requested information or click on a link, allowing hackers to easily obtain user information.
How to avoid or stop email spoofing?
Following are some of effective ways to stop email spoofing:
- Enable spam filters: Spam Filters (powered by Apache SpamAssassinTM) is an automated spam filtering system that identifies and filters spam messages using a variety of techniques. Read this article to learn how to use Spam Filters to prevent unwanted e-mail.
- Implement Sender Policy Framework (SPF), domainkeys identified mail (DKIM), and Domain-based Message Authentication, Reporting & Conformance (DMARC). Check this article on How to configure SPF and DKIM in email deliverability setting using cPanel.:
- Sender Policy Framework (SPF): an authentication protocol that lists IP addresses in a DNS TXT record that are permitted to send email on behalf of domains.
- Domainkeys identified mail (DKIM): A method of assigning a private key to an email that is leaving the server so that the receiving server can use the key for verification.
- Domain-based Message Authentication, Reporting & Conformance (DMARC):A protocol that determines the authenticity of an email message using both SPF and DKIM.
- Use Secure Email Gateway (SEG) software, such as Barracuda, to monitor emails as they are sent and received in order to provide predelivery protection by blocking email-based threats before they reach a mail server.Learn how to enable and configure the Barracuda Spam Firewall to reduce spam and protect your domain from malicious e-mail threats.
Article Details
- Product: All accounts
- Level: Beginner
Grow Your Web Business
Subscribe to receive weekly cutting edge tips, strategies, and news you need to grow your web business.
No charge. Unsubscribe anytime.
Did you find this article helpful? Then you'll love our support. Experience the A2 Hosting difference today and get a pre-secured, pre-optimized website. Check out our web hosting plans today.